Storage Vendor QNAP Forces Update After Ransomware Hits 3600 Devices
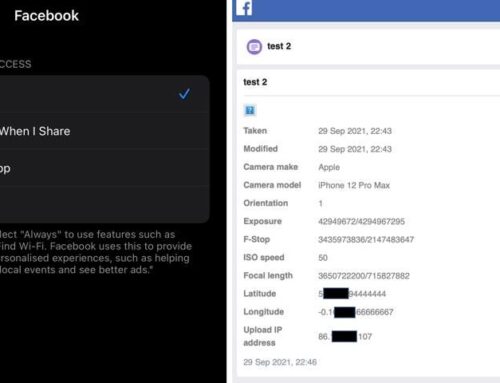
Ransomware criminals have launched a campaign that https://lkp.ndu.edu.ua/ infected and encrypted data on thousands of network attached storage devices made by Taiwan-based QNAP. The company took drastic action to prevent further attacks, remotely force-installing an update on users’ devices in the middle of the night.
The Deadbolt ransomware started seeking out vulnerable QNAP NAS devices just three days ago, infecting just under 3700. A warning screen left behind by Deadbolt claims that users aren’t being targeted personally. Instead, the attackers blame “the inadequate security provided by [their] vendor (QNAP).”
Two different ransom demands were made. Individual users were told they could pay 0.03 Bitcoin — about $1100 U.S. dollars at today’s exchange rat — to receive a decryption key that would unlock their files.
Another offer was made to QNAP. Deadbolt offered to provide a master key that would decrypt all victims’ files for a much steeper 50 bitcoin, or roughly $1.8 million. As a bonus, the attackers would also hand over information about the previously-undiscovered exploit that was used to infect these QNAP devices.
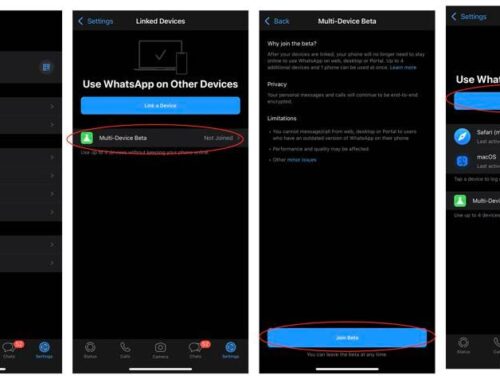
QNAP warned its customers of the attacks the day after they began. The company issued a statement and recommended that users verify their security settings immediately. Several configuration changes were recommended to keep the Deadbolt ransomware at bay. QNAP also strongly advised users to install the latest firmware for their devices.
Historically, though, not everyone is in a hurry to update. Some merely find it inconvenient, but others have legitimate concerns about software updates causing unwanted disruptions.
Considering the situation to be grave, QNAP opted to force-update vulnerable devices. While undeniably beneficial in terms of disrupting the Deadbolt attacks, the update had an undesired effect on some users’ systems.
Some lost access to some of the drives on which their data was stored. Others who had had already http://cel.cus.ac.in/ been hit by the ransomware and were trying to decrypt found that the decryption process was now broken.
This is an incredibly difficult situation for both vendors and users. Certainly given QNAP’s market share and the relatively low number of infections at the time factored in to the decision.
https://esquel.org.ec/es/
Still, it’s impossible not to sympathize with the unfortunately few who are dealing with a new set of problems following the update. It’s just one of the many side effects of the never-ending battle against global malware.https://dpmis.dost.gov.ph/