Ransomware on a Rampage; a New Wake-Up Call
Ransomware is on a rampage targeting industry and organizations. It is also and creating significant cybersecurity challenges. Ransomware olxslot gacor is a type of malware cyber-attack where key files are encrypted encryption by hackers that renders data inaccessible to the victim. It is a criminal extortion tool and after an attack has occurred, the hackers will promise to restore systems and data when ransom is paid by the victims.
The use of ransomware by hackers to leverage exploits and extract financial benefits is not new. https://cobija.unitepc.edu.bo/ Ransomware has been around for over 2 decades, (early use of basic ransomware malware was used in the late 1980s) but as of late, it has become a trending and more dangerous cybersecurity threat. The inter-connectivity of digital commerce and expanding attack surfaces have enhanced the utility of ransomware as cyber weapon of choice for bad actors. Like bank robbers, cybercriminals go where the money is accessible. And it is now easier for them to reap benefits from extortion. Hackers can now demand cryptocurrencies payments or pre-paid cards that can be anonymously transacted. Those means of digital payments are difficult to trace by law enforcement.
But it is not just the financial gains, while hackers can use ransomware to extort, it can also be https://socialinnovationacademy.org/career/ employed to harass and demonstrate vulnerabilities to critical infrastructure. In this sense, state actors and/or criminal gangs can use ransomware as an instrument of geo-political power. Hackers often operate in tacit support by nation state https://africaneye.soscodesoftware.com/ actors and criminal enterprises acting in cahoots. The use of ransomware against critical infrastructures has certainly elevated the issue to global national security levels.
https://teamexuberance.org/about/
The Targets (and Costs) of Ransomware Attacks:
The current state of cyber-affairs is an especially alarming one because ransomware attacks are growing not only in numbers, but also in the financial and reputational costs to businesses and organizations. Three statistics stand out that highlight ransomware trends and implications:
15 Innovative AI Companies Driving Exponential Shifts In Their Respective Sectors
Google Dismantling Health Division
As Streaming Competition Heats Up, YouTube TV Adds More Sports Channels
1) a recent report from Trend Micro has found that 84% of US organizations have reported phishing or ransomware security incidents in the last 12 months. 84% of Organizations Experienced Phishing & Ransomware Type Threats in the Past 12 Months (yahoo.com)
2) according to a report from Palo Alto Networks’ Unit 42 security consulting group, the average ransomware payment climbed 82% to a record $570,000 in the first half of 2021 from $312,000 in 2020. Ransomware criminals’ demands rise as aggressive tactics pay off | Fox Business https://hrm.stamforduniversity.edu.bd/
3) and as a harbinger of things to come, the firm Cybersecurity Ventures estimates that Ransomware Costs Expected to Reach $265 Billion by 2031. The Cybersecurity Ventures analysis predicts that there will be a new attack every 2 seconds as ransomware perpetrators progressively refine their malware payloads and related extortion activities. Global Ransomware Damage Costs Predicted To Exceed $265 Billion By 2031 (cybersecurityventures.com)
In many cases a ransomware hack can cripple a company’s systems and networks and cause panic and confusion. Companies and organizations who depend on logistics planning and supply chain coordination to operate are particularly at risk. Ransomware malware is designed so it can rapidly spread across a company’s or organization’s computers and networks. Success for hackers does not always depend on using the newest and most sophisticated malware. It is easy for a hacker to do. In most cases, they rely on the most opportune target of vulnerability, especially with the ease of online attacks. Hackers have a large library of malware to choose from as it is estimated that there over 120 separate families of ransomware.
A Short Summary of Ransomware Attacks:
In 2013, hackers used a ransomware called CryptoLocker that required victims to pay funds to recover their vital files. Four year later in 2017, the use of ransomware heightened with an attack called WannaCry. The worldwide WannaCry attack in 2017 was viewed by many (especially in the media) as a wake-up call to the disruptive implications of ransomware. The WannaCry ransomware was self-replicating and spread swiftly reaching over one hundred countries. In various countries, many industries, organizations, and government agencies were victimized. The ransomware disrupted hospital, schools, organizational and company networks that were not well protected and up to date. Those industries were low hanging fruit for hackers. The attacks did not turn out to be as lethal as originally feared, but it certainly demonstrated the global vulnerabilities associated with inter-connected networks and devices.
Despite CryptoLocker, WhiteRose, WannaCry, Petya, and many other high-profile ransomware attacks, the wake-up call was not heeded. Industry, organizations, and governments did little to fortify and defend against such attacks. Earlier this year, the Darkside ransomware gang breached the Colonial Pipeline shutting down their 5,500-mile natural gas pipeline for a week. As a result, gas stations across the Eastern coast of the United States ran out of gas and many services and product supply lines were disrupted.
In July, a ransomware attack by the Revil criminal ransomware-as-a-service gang infected an estimated 1,500 businesses with ransomware. the attackers found a vulnerability that they exploited in the update mechanism used by the IT services company Kaseya VSA. REvil, a decryption key to those hit by the attack in return for a $70 million payment. Also this Summer, hackers targeted and disrupted operations at JBS, the world’s largest meat supplier.
During the past couple of years, healthcare and hospitals were targeted by ransomware attacks. In October 2020, the University of Vermont Health Network was hit by a ransomware attack and their systems couldn’t access electronic health records for nearly a month. It was determined that every computer at UVM Medical Center was found to be infected with malware. The pandemic revealed the health risks of hospital ransomware attacks – The Verge
Many hospitals (like UVM) were vulnerable because they tended to have poor cybersecurity and use many networks and devices that allow for a bigger attack surface. Hackers took advantage over stressed conditions caused Covid 19 to escalate ransomware attacks. Because vital medical facilities cannot afford to shut down, they often comply with ransomware demands to maintain operations.
Unfortunately, for hackers’ soft targets are plentiful, especially in the healthcare, financial, and manufacturing industries, and we can expect to see more such attacks because the vulnerabilities to many networks remain open and accessible to hackers.
And as they continue to receive payments from victims, hackers have become even more aggressive in their illicit activities. A recent study by Accenture highlighted how Ransomware actors are growing bolder and sophisticated in their attacks on OT and IT environments. The report noted that criminal gangs cooperate and share commercial hacking tools (such as the pirated Cobalt Strike malware) via the Dark Web. Their targets include critical infrastructure sectors, including manufacturing, financial, energy, and agriculture. The study also says that hackers are using more aggressive high-pressure tactics to escalate infection consequences and that often they deploy multiple pressure points at once to extract ransom payments. In some cases, they are also using double and triple extortion threats. Ransomware attackers are growing bolder and using new extortion methods – TechRepublic
The U.S. Government Response to Ransomware
detail of an american government pin. E Pluribus Unum.
getty
The national security importance regarding ransomware attacks is evident in recent policy proclamations by the White House and other government agencies. In June, Anne Neuberger, Deputy Assistant to the President and Deputy National Security Advisor for Cyber and Emerging Technology, published an open letter to business leaders about the significant threat of ransomware attacks. The letter urged companies to take the threat of ransomware seriously and adopt cybersecurity practices that match this threat. It said: “The private sector also has a critical responsibility to protect against these threats. All organizations must recognize that no company is safe from being targeted by ransomware, regardless of size or location. But there are immediate steps you can take to protect yourself, as well as your customers and the broader economy. Much as our homes have locks and alarm systems and our office buildings have guards and security to meet the threat of theft, we urge you to take ransomware crime seriously and ensure your corporate cyber defenses match the threat.” The open letter set excellent guidelines and provided sound advice on bolstering defenses against ransomware. Memo-What-We-Urge-You-To-Do-To-Protect-Against-The-Threat-of-Ransomware.pdf (whitehouse.gov)
Also, the U.S. government is also focusing on ransomware as a law enforcement issue. A new Ransomware and Digital Extortion Task Force was created several months ago by the Department of Justice (DOJ) to help track cyberattacks and digital extortion schemes and combat them. Department Of Justice Creates New Task Force To Take On Ransomware Attacks (forbes.com)
Preventive Actions to Help Mitigate Ransomware Attacks:
Ransomware Cloud painted with chalk on blackboard.
getty
While it is true that anyone and everyone is vulnerable to ransomware attacks, there are available protections and defenses for helping mitigate those threats. It starts with have a risk management strategy and being proactive. First (and foremost) patching and updating of software vulnerabilities must be current. Unfortunately, many companies and organizations are slow, and in many cases, negligent on the update of patches that would prevent breaches.
Also, some basic precautions can help address threats, these include training employees to recognize malware and phishing threats, disabling macro scripts, cloaking data, and keeping systems and applications updated. Identity management policies and software are also practical tools to employ. If you end up victimized by a breach, be sure to have an incident response plan in place. That plan should also include potentially contacting law enforcement to assist in recovering files and investigating who is doing the hacking.
Cyber-hygiene is another important element for combatting ransomware. Phishing is a preferred method for hackers and simple advice is to not click on files that you do not know. Because of hacker tools that employ automated phishes and quality graphics that can mimic banks and businesses, pay careful attention to the URLs of websites to make sure they are legitimate and not spoofs. Especially watch for spam fake job offers, invoices for items you did not order, and messages from your company that seem out of place. Also, you should make it a habit to verify email senders are who they say they are and exercise caution when opening any email attachments.
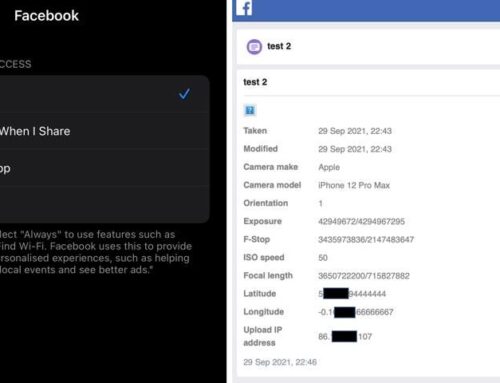
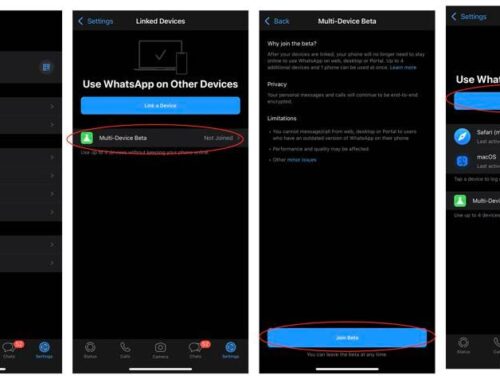
Check your permissions on your apps to see what data they are accessing. If it is not something you authorized, be sure to revoke those access rights and to clean out your cookies.
Companies and individuals should employ anti-malware & anti-ransomware platforms, and technologies to guard your devices such as multi-factor authentication, firewalls, and email filters. Emerging technologies such as machine learning (ML) and artificial intelligence (AI) offer software tools that can detect anomalies, provide user behavioral analytics, and help mitigate threats. ML and AI are viable options for companies to consider for fortifying their security.
Everyone online, companies and consumers, should follow the important rule of backing up important or sensitive files! Proper backup procedures cost little in expense and time and can be an insurance policy for maintain company operations flowing in the case of a breach.
If you are a small or medium company that lacks resources, Managed Security Services (MSS) and Managed Service Providers (MSP) are options to consider using for both prevention and incident response. Many firms can monitor networks, provide enabling cybersecurity technologies, and threat assessments. MSS makes economic sense for many industries and businesses, which do not have (or can afford) the internal subject matter expertise or capabilities to handle increasingly sophisticated breaches. Paradoxically, some of MSS and MSPs have themselves been targeted by ransomware attacks. But in today’s world, everyone is a target.
Risk Management Resources for Ransomware:
risk management concept hand drawn on chalkboard
getty
The White House Open letter open letter set excellent guidelines and provided sound advice on bolstering defenses against ransomware. Below are additional useful government resources from DHS/CISA, NIST and others to learn more about ransomware threats, risk management, and how to build a more resilient security posture.
Protecting Sensitive and Personal Information from Ransomware-Caused Data Breaches (cisa.gov)
The sobering reality is that ransomware is on a rampage. Ransomware will continue to be a destructive threat because there are so many available soft targets. We live in an increasingly hyper-connected world that impacts all aspects of our lives. From now and onward, managing and protecting data will be a security imperative for every industry and organization.
Awareness and understanding the ransomware threat can help address many of the cybersecurity challenges. Emerging cybersecurity technologies, mitigation tools, and protocols can help limit the exploding trend of ransomware attacks. Taking pro-active measures to protect systems, networks, and devices, and be more resilient, need to be part of a new wake-up call.